Giới thiệu
Đại lý Cửa cuốn Austdoor Hồ Chí Minh luôn mong muốn đáp ứng mọi dịch vụ của khách hàng về một sản phẩm cửa cuốn hiện đại, tiên tiến nhất với đội ngũ nhân viên dày dạn kinh nghiệm. Chúng tôi đã cung cấp một dịch vụ lắp đặt, bảo trì bảo dưỡng cửa cuốn Austdoor tại Hồ Chí Minh và toàn khu vực Miền Nam, với mong muốn được cung cấp dịch vụ chất lượng cùng các chính sách bảo hành tốt nhất, nhanh nhất, giá cả hợp lý nhất cho khách hàng sử dụng. Dịch vụ Lắp đặt cửa cuốn Austdoor Hồ Chí Minh luôn được các đối tác lớn tin tưởng sử dụng trong nhiều năm qua, cùng với bảng báo giá cửa cuốn Austdoor 2024 của tập đoàn Austdoor Miền Nam luôn mang đến cái nhìn trực quan hơn về các chi phí cần đầu tư của bạn.
Sản phẩm cửa cuốn Austdoor với tính năng đồng bộ cao, được sản xuất và lắp ráp tại nhà máy, giúp cửa vận hành êm ái ổn định và bền vững trong mọi thời tiết.
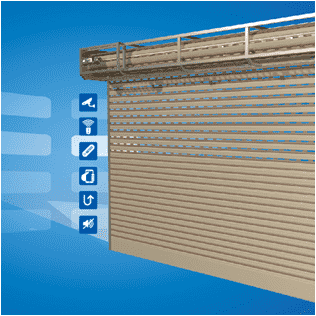
Austdoor được thiết kế hiện đại và trang nhã, có khả năng tạo hình trên mọi bề mặt, chất liệu, đa dạng về chủng loại mẫu mã và màu sắc, hài hòa với thiên nhiên sống.
Sản phẩm Austdoor sử dụng công nghệ ARC, nhằm ngăn chặn kẻ gian bằng việc chống sao chép mã hệ thống, nhằm bảo vệ an toàn cho ngôi nhà và gia đình của bạn.
Cửa cuốn Austdoor với 3 cấp độ bảo vệ hệ thống: bộ đảo chiều có dây, bộ đảo chiều không dây, bộ sensor hồng ngoại. Giúp cho ngôi nhà của bạn An toàn tuyệt đối.
Austdoor Hỗ trợ dịch vụ
-
Hotline
0932.653.889 - 0971.899.529 -
-
Thời làm việc
8h - 20h